Collection of cheat sheets useful for security and pentesting. Focus on web, mobile, cloud, active derictory (AD), learning platforms, tools, etc.
This repo is the updated version from awesome-pentest-cheat-sheets.
Your contributions and suggestions are heartily welcome. Please check the Contributing Guidelines for more details.
- Cybersecurity Conference Directory - All Cybersecurity, InfoSec & IT Conferences and Events
- Confsec - List of Security Events 2024
- InfoCon - The Hacking Conference Archive
- Awesome Security Talks - Curated list of Security Talks and Videos
- The Hackers' Choice Tips & Tricks Cheatsheet
- Docker Cheat Sheet
- OSX Command Line Cheat Sheet
- PowerShell Cheat Sheet - SANS PowerShell Cheat Sheet from SEC560 Course (PDF version)
- Rawsec's CyberSecurity Inventory - An open-source inventory of tools, resources, CTF platforms and Operating Systems about CyberSecurity. (Source)
- Regexp Security Cheat Sheet
- Security Cheat Sheets - A collection of security cheat sheets
- Unix Commands Cheat Sheet
- Linux File Permissions Cheat Sheet
- DostoevskyLabs' Pentest notes - Pentest Notes collection from DostoevskyLabs
- Thick Client Pentest Checklist - Pentest Checklist for Thick-Client Penetration Tests
- HauSec's Pentesting Cheat sheet - Pentest Cheat sheet from HauSec
- Mobile App Pentest Cheat Sheet - Collection of resources on Apple & iOS Penetration Testing
- Mobexler - Customised virtual machine, designed to help in penetration testing of Android & iOS applications.
- Android Pentest Checklist Xmind - Xmind mindmap for Android Penetration Tests
- MASTG - OWASP Mobile Application Security Testing Guide [PDF]
- Android Pentesting Checklist - Case-by-case Checklist for Android Pentests
- Android Pentesting Cheat sheet - Android Pentesting Resources #1
- HackTricks - Android Pentesting - HackTricks Collection of Android Pentesting
- iOS Pentest Checklist - Checklist for iOS/IPA Penetration Tests
- Hacktricks iOS Checklist - Another Checklist for iOS/IPA Penetration Tests | Hacktricks Cloud
- PentestGlobal IOS gitbook - Gitbook about iOS Pentesting
- Can i jailbreak? - List of each jailbreak needed for each iOS version
- Jailbreaks.app - Downloads for Odyssey, Taurine Jailbreaks
- Awesome Kubernetes (K8s) Security - Collection of Kubernetes security resources
- Kubetools - Kubernetes security tools
- HackingKubernetes - Collection of Kubernetes Pentesting Resources
- Kubernetes Goat - Vulnerable-by-Design cluster environment for training
- KubePwn - Another Collection of resources about Kubernetes security
- HackTricks - Kubernetes Pentesting - HackTricks Collection of Kubernetes Pentesting
- Awesome Azure Pentest - A curated list of useful tools and resources for penetration testing and securing Microsofts cloud platform Azure.
- HackTricks - Azure Pentesting - HackTricks Collection of Kubernetes Pentesting
- Active Directory Exploitation Cheat Sheet - Cheat sheet for Active Directory Exploitation
- OSCP Active Directory Cheat Sheet - Cheat sheet for Active Directory Attacks used in OSCP
- WADComs - Interactive cheat sheet - list of offensive security tools and their respective commands to be used against Windows/AD environments.
- HackTricks - Active Directory Pentesting - HackTricks Collection of Active Directory Pentesting
- GOAD - Vulnerable-by-Design Active Directory environment
- Ultimate BloodHound Guide - The Ultimate Guide for BloodHound Community Edition (BHCE)
- Windows Red Team Cheat sheet - Windows for Red Teamers Cheat Sheet (Moved to wiki)
- Resource Collection #1 - Collection of Active Directory Pentesting resources #1
- Resource Collection #2 - Collection of Active Directory Pentesting resources #2
- Resource Collection #3 - Collection of Active Directory Pentesting resources #3
- Resource Collection #4 - Collection of Active Directory Pentesting resources #4
- Google Dorks - Google Dorks Hacking Database (Exploit-DB)
- Shodan - Shodan is a search engine for finding specific devices, and device types, that exist online
- ZoomEye - Zoomeye is a Cyberspace Search Engine recording information of devices, websites, services and components etc.
- Amass - OWASP Network mapping of attack surfaces and external asset discovery using open source information
- Censys - Similar to shodan, search engine for specific devices including IoT
- enum4linux-ng - Python tool for enumerating information from Windows/Samba systems
- 0xdf - SMB Enumeration - 0xdf's SMB Enumeration Cheat Sheet
- OSCP Enumeration Cheat sheet - Cheat sheet for Enumeration for OSCP Certificate
- CrackMapExec Cheatsheet - Cheat sheet for CrackMapExec (CME)
- Empire Cheat Sheet - Empire is a PowerShell and Python post-exploitation framework
- Exploit Development Cheat Sheet - @ovid's exploit development in one picture
- Java Deserialization Cheat Sheet - A cheat sheet for pentesters about Java Native Binary Deserialization vulnerabilities
- Local File Inclusion (LFI) Cheat Sheet #1 - Arr0way's LFI Cheat Sheet
- Local File Inclusion (LFI) Cheat Sheet #2 - Aptive's LFI Cheat Sheet
- Metasploit Unleashed - The ultimate guide to the Metasploit Framework
- Metasploit Cheat Sheet - A quick reference guide (PNG version)(PDF version)
- PowerSploit Cheat Sheet - PowerSploit is a powershell post-exploitation framework
- PowerView 2.0 Tricks
- PowerView 3.0 Tricks
- PHP htaccess Injection Cheat Sheet - htaccess Injection Cheat Sheet by PHP Secure Configuration Checker
- Reverse Shell Cheat Sheet #1 - Pentestmonkey Reverse Shell Cheat Sheet
- Reverse Shell Cheat Sheet #2 - Arr0way's Reverse Shell Cheat Sheet
- SQL Injection Cheat Sheet - Netsparker's SQL Injection Cheat Sheet
- SQLite3 Injection Cheat Sheet
-
Awesome Windows Post Exploitation - Collection of resources for Windows Post-Exploitation
-
HackTricks - Post Exploitation - HackTricks Collection of Post-Exploitation
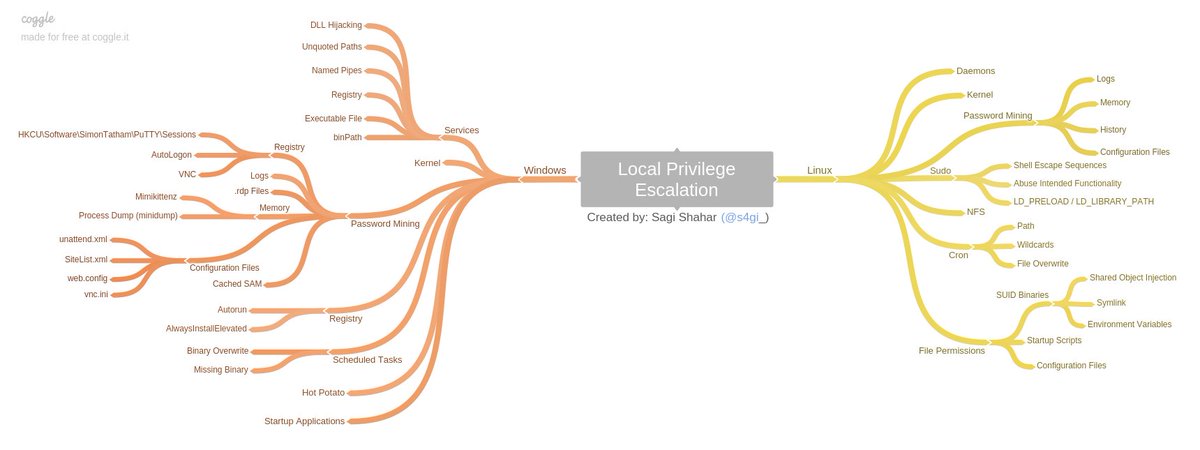
- Windows / Linux Local Privilege Escalation Workshop - The Privilege Escalation Workshop covers all known (at the time) attack vectors of local user privilege escalation on both Linux and Windows operating systems and includes slides, videos, test VMs.
- Basic Linux Privilege Escalation - Linux Privilege Escalation by @g0tmi1k
- linux-exploit-suggester.sh - Linux privilege escalation auditing tool written in bash (updated)
- Linux_Exploit_Suggester.pl - Linux Exploit Suggester written in Perl (last update 3 years ago)
- Linux_Exploit_Suggester.pl v2 - Next-generation exploit suggester based on Linux_Exploit_Suggester (updated)
- Linux Soft Exploit Suggester - linux-soft-exploit-suggester finds exploits for all vulnerable software in a system helping with the privilege escalation. It focuses on software packages instead of Kernel vulnerabilities
- checksec.sh - bash script to check the properties of executables (like PIE, RELRO, PaX, Canaries, ASLR, Fortify Source)
- linuxprivchecker.py - This script is intended to be executed locally on a Linux box to enumerate basic system info and search for common privilege escalation vectors such as world writable files, misconfigurations, clear-text passwords and applicable exploits (@SecuritySift)
- LinEnum - This tool is great at running through a heap of things you should check on a Linux system in the post exploit process. This include file permissions, cron jobs if visible, weak credentials etc.(@Rebootuser)
- linPEAS - LinPEAS - Linux Privilege Escalation Awesome Script. Check the Local Linux Privilege Escalation checklist from book.hacktricks.xyz
- MimiPenguin - A tool to dump the login password from the current linux desktop user. Adapted from the idea behind the popular Windows tool mimikatz.
- PowerUp - Excellent powershell script for checking of common Windows privilege escalation vectors. Written by harmj0y (direct link)
- PowerUp Cheat Sheet
- Windows Exploit Suggester - Tool for detection of missing security patches on the windows operating system and mapping with the public available exploits
- Sherlock - PowerShell script to quickly find missing software patches for local privilege escalation vulnerabilities
- Watson - Enumerate missing KBs and suggest exploits for useful Privilege Escalation vulnerabilities
- Precompiled Windows Exploits - Collection of precompiled Windows exploits
- Metasploit Modules
- post/multi/recon/local_exploit_suggester - suggests local meterpreter exploits that can be used
- post/windows/gather/enum_patches - helps to identify any missing patches
- Web Pentest Checklist - Checklist for Web Application Penetration Tests
- OWASP VWAD - Registry of all known vulnerable web applications currently available.
- SQL Injection Cheatsheet - PortSwigger SQL Injection Cheat Sheet
- Cross-Site-Scripting Cheat sheet PortSwigger Cross-Site-Scripting (XSS) Cheat sheet
- Google CSP Evaluator Google's CSP Evaluator (Chrome Extension)
- Awesome Web Hacking - Collection of resources for Web Pentesting #1
- Awesome Web Security - Collection of resources for Web Pentesting #2
- XSS Polyglot Payloads #1 - Unleashing an Ultimate XSS Polyglot list by 0xsobky
- XSS Polyglot Payloads #2 - @filedescriptor's XSS
- Browser's-XSS-Filter-Bypass-Cheat-Sheet- Excellent List of working XSS bypasses running on the latest version of Chrome / Safari, IE 11 / Edge created by Masato Kinugawa
- Binary Exploitation Red Team Notes - ired.team notes for Binary Exploitation
- Binary Exploitation Notes - Ir0nstone's Binary Exploitation Notes
- Sticky Notes Binary Exploitation - Sticky Notes colletion for Binary Exploitation
- checksec.py - Cross-Platform CheckSec Tool for checking binary security properties
- HackTricks - Binary Exploitation - HackTricks Collection of Binary Exploitation
- Liveoverflow - Binary Exploitation LiveOverflow's Binary Exploitation youtube playlist
- PwnTools Cheat sheet - Cheat sheet for PwnTools python library
- pwndbg Cheat sheet - Cheat sheet for pwndbg GDB plug-in
- GDB PEDA Cheat sheet - Cheat sheet for PEDA GDB plug-in
- Hack The Box :: Penetration Testing Labs - Leading penetration testing training labs platform
- TryHackMe - Free online platform for learning cyber security & penetration testing
- OWASP Vulnerable Web Applications Directory Project (Online) - List of online available vulnerable applications for learning purposes
- Pentestit labs - Hands-on Pentesting Labs (OSCP style)
- Root-me.org - Hundreds of challenges are available to train yourself in different and not simulated environments
- Vulnhub.com - Vulnerable By Design VMs for practical 'hands-on' experience in digital security
- Damn Vulnerable Xebia Training Environment - Docker Container including several vurnerable web applications (DVWA,DVWServices, DVWSockets, WebGoat, Juiceshop, Railsgoat, django.NV, Buggy Bank, Mutilidae II and more)
- OWASP Vulnerable Web Applications Directory Project (Offline) - List of offline available vulnerable applications for learning purposes
- Vulnerable SOAP Web Service - a vulnerable SOAP web service lab environment
- Vulnerable Flask Web App - vulnerable Flask Web App lab environment
- Awesome BugBounty Tools - A curated list of various bug bounty tools
- bug-bounty-platforms - Open-Sourced Collection of Bug Bounty Platforms
- m0chan - Bug Bounty Methodology - m0chan's Bug Bounty Methodology Collection
- NahamSec - Resources for Beginners - NahamSec's Resources for Beginner Bug Bounty Hunters Collection
- AllAboutBugBounty - BugBounty notes gathered from various sources
- Bug-Bounty-Resources - Collection of Bug Bounty Resources #1
- Bug-Bounty-Resources - Collection of Bug Bounty Resources #2
- Ryan John Bug Bounty Playlist - Collection of Ryan John's BugBounty videos (11h Full Course Video)
- LiveOverFlow Bug Bounty Playlist - Collection of LiveOverflow's Bug bounty videos
- BBRE Podcast - Bug Bounty Reports Explained Podcast
- Critical Thinking Podcast - Critical Thinking Bug Bounty Podcast
- Nmap Cheat Sheet
- SQLmap Cheat Sheet
- SQLmap Tamper Scripts - SQLmap Tamper Scripts General/MSSQL/MySQL
- VIM Cheatsheet
- Wireshark Display Filters - Filters for the best sniffing tool
- revshells.com - Reverse shell payload generator (Source code)
- Segfault - Segfault: Free disposable root servers (by @THC)
- suip.biz - Various free online pentesting tools like nmap, wpscan, sqlmap (...)
- XSS'OR Encoder/Decoder - Online Decoder/Encoder for testing purposes (@evilcos)
- WebGun - WebGun, XSS Payload Creator (@brutelogic)
- Hackvertor - Tool to convert various encodings and generate attack vectors (@garethheyes)
- JSFiddle - Test and share XSS payloads, Example PoC
- Fuzzdb - Dictionary of attack patterns and primitives for black-box application testing Polyglot Challenge with submitted solutions
- SecList - A collection of multiple types of lists used during security assessments. List types include usernames, passwords, URLs, sensitive data grep strings, fuzzing payloads, and many more
- Bug Bounty Reference - huge list of bug bounty write-up that is categorized by the bug type (SQLi, XSS, IDOR, etc.)
- Write-Ups for CTF challenges
- Facebook Bug Bounties - Categorized Facebook Bug Bounties write-ups
- wifite2 - Full automated WiFi security testing script
- Docker Security Cheat Sheet - The following tips should help you to secure a container based system (PDF version)
- Windows Domain Hardening - A curated list of awesome Security Hardening techniques for Windows
- JavaScript Cheat Sheet - Learn javascript in one picture (Online version) (PNG version)
- Python Cheat Sheet #1 - Learn python3 in one picture (PNG version)
- Python Cheat Sheet #2 - Learn python3 in one picture (Online version) (PNG version)
- Python Snippets Cheat Sheet - List of helpful re-usable code snippets in Python